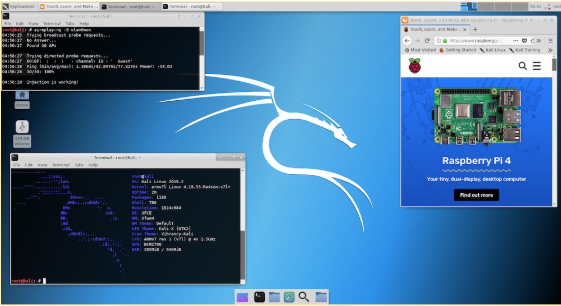
Created, maintained, and funded by Offensive Security, Kali is an advanced penetration testing solution packaged in one convenient Linux OS. Offensive Security also offers training on general cybersecurity research practices and how to use Kali Linux. Read on to learn more about Kali Linux and why it might be the right OS for you, or skip to the end for the Pi 4 download link.
What is Penetration Testing?
A penetration test, or pentest for short, is meant specifically to find security weaknesses in software that could allow an external actor access to a computer or network’s data.
Today, the term “hacking” can mean anything from making something cool out of random parts to breaking into a computer system or network. Even the latter can be done in different methods that do not require advanced software knowledge, such as social engineering or phishing attacks. Ethical, or “white hat”, hacking refers to finding exploits and vulnerabilities in a system in order to fix them or researching methods to do so. They differ from “black hat” hackers because they report the issues instead of abusing them.
Included in this broad term is penetration testing. Kali has many tools (more than 300) for this very purpose. Among these are Metasploit, a framework for hacking tools, THC Hydra, a fast, brute-force password cracker, the Social Engineer Toolkit, an application that facilitates the creation and sending of malicious emails, and Aircrack-ng, a Wi-Fi network hacking tool.
Though these tools may sound scary or inherently malicious, they can be a vital asset in securing your private information and network security.
If any of your projects transmit data across Wi-Fi, you could accidentally be putting your network at risk. This is especially important when using Pis in a business or commercial network where more valuable data can attract potential hackers. You may have forgotten to change your Pi’s default username and password, or maybe your Pi automatically opens every email it receives and forwards it to someone else. Though seemingly safe, these are security vulnerabilities that risk your network’s integrity should someone choose to exploit them.
Why Pick Kali Linux for Pi 4?
We’ve gone over what Kali Linux can do and why it is important, but why run it on a Raspberry Pi 4?
Advanced Specs
First of all, Pi 4 is pretty beefy for a single board computer. Though it is about the size of a portable SSD, this new Pi can support two 4K monitors simultaneously, 4 gigabytes of RAM, and USB 3.0 ports. This makes it an excellent choice for a portable pentest setup, and it can be included in your workstation without much rearranging necessary.
Perfect for Experimentation
Given the Pi 4’s specifications and accessible cost, it is a good computer for budding cybersecurity researchers to start with. Installing a new operating system on your work computer may not be the wisest decision, after all. The Pi 4 will let you freely explore the world of ethical hacking without much risk to your more expensive hardware.
Future 64-bit Support
Though only a 32-bit version is currently supported, a 64-bit version of Kali is available for the Pi 3 and is in the works for the Pi 4. It is unclear if a 64-bit version of Raspbian will be available, so this will be one of the few operating systems to support a 64-bit version.
Hardware and Peripherals
Combining the tools provided by Kali with the Pi 4’s GPIO pins leads to endless possibilities! You could make a password hacking robot that drives around the office telling your employees how weak their passwords are, an automated phishing drill to see how coworkers would react to a real attack, or you could just try to hack into your own network by collecting data packets from your IoT projects around the house.
Download Kali Linux and Help Links
To download a Kali image, go to the official download page and scroll down to the Raspberry Pi Foundation tab. Download the Pi 4 version, and follow our guide for installing OS images on a microSD card. After that, boot up your Pi and log in with “root” as the username and “toor” as the password. Lastly, remember to change your default login information. For in-depth help, check out the Kali Linux Docs and the Kali Linux Community.
Cover image courtesy of Offensive Security.